Without a sound knowledge of compliance requirements, most CISOs tend to implement fractured or ad-hoc solutions which only touch a portion of the organization’s data or only certain segments of the business. Ambiguous ownership of these efforts tends to foster poor vision, undefined goals, and inaccurate measurements, which ostensibly leads to poor quality business decisions.
In developing a broad strategy for data privacy and compliance, organizations gravitate toward two primary methods: leveraging a compliance framework such as NIST or CIS to provide discrete, actionable steps towards maturity, or they seek out a solution provider offering some kind of compliance widget or service.
In the first scenario, compliance frameworks provide a good foundation for meeting their described outcomes but recall that most organizations are subject to dozens of regulations. Obtaining all the requisite frameworks and condensing them into a single, monolithic guidebook is rarely feasible, and seldom effective. Trying to keep this compliance casserole updated becomes a full-time job for entire departments depending on the organization’s industry, markets, and complexity.
It’s also worth noting here that an organization can be fully compliant and still suffer data loss and the subsequent aftermath. While complying with a specific regulation’s parameters may help to lessen the legal or financial impact, it does little to soften the blow to the organization’s reputation and loss of customer trust. Posting the company’s internal pricing models on social media may not violate a regulation, but it clearly isn’t a good business move.
Regarding the second option, vendor solutions are appealing for a number of reasons. Leaning on the expertise of a partner fosters an element of shared risk, and some vendors outright guarantee their services. Further, the vendor’s own mastery of the subject matter means that data privacy leaders do not need to “staff up” to meet the challenges of an evolving compliance landscape.
However, it’s also worth noting that results are only as good as the configuration of the technology and the SLAs of the provider. Nearly every data loss prevention technology comes with pre-canned templates designed to meet basic requirements of regulations such as HIPAA or PCI, but templates are designed as a one-size-fits-all solution. They are not tailor-made to the specific risk-reduction goals of the organization. To compensate, vendors will often supplement their solutions with a configuration service, but their expertise is still focused on technology and not the client organization. The vendor may have a solid grasp of GDPR, for example, but remains comparatively immature when it comes to understanding how the organization transacts business.
That’s not to say that vendor results are bad. They offer a solid starting point and are certainly better than having nothing in place at all. But CISOs who adopt a “set-it and forget-it” mindset are quickly inundated with false positives, and worse, they have little assurance about unidentified incidents where critical data has flown out the door due to sub-par configuration or a lack of training. If data stakeholders are serious about protecting their sensitive information, they must look beyond merely checking boxes off a compliance framework or acquiring more technology.
Fixing these complex issues requires a comprehensive strategy that can address everything from data usage and data classification all the way through the continued maintenance and tuning of technical controls, such as DLP or encryption. CISOs must shift their mindset from managing software suites to building, maintaining, and maturing a comprehensive Data Risk Management (DRM) Program.

Learn more about data risk management, our in-depth expertise, and our DRM Program Build offering.
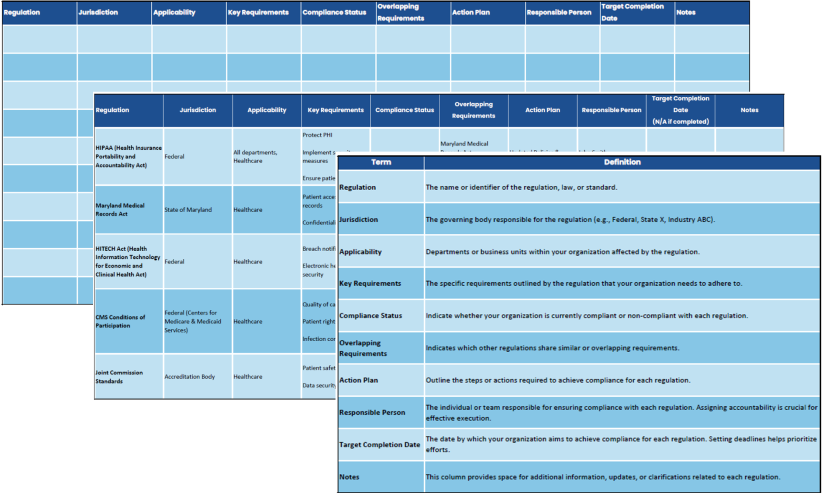
Consider identifying these common features that are part of nearly every compliance regulation:

How was this regulation developed? Has the regulation been revised over the years? Was there a compelling industry or government-related event that drove this regulation to be created? Knowing the background of the regulations can provide a good sense of why the law exists and may inform CISOs or Data Protection Officers about the intent(s) of those who created the law.

What standards exist for data usage and handling?
Nearly every regulation contains parameters about data usage and handling. This is more than just standard cybersecurity control. These provisions can call out the ways in which organizations acquire, create, store, access, share, archive, retain, and delete information. Data reduction is often a component of data handling and involves decreasing the amount of non-critical information being collected and stored. Data privacy leaders should reshape business processes so only information relevant to their services is collected to begin with.

What reporting is required?
Many regulations have show-cause or chain-of-custody type language that dictates organizations must not only protect data, but they must be able to prove it from a legal standpoint. In some data breaches, organizations have received lesser penalties for their ability to prove that while data was breached or stolen, it was encrypted at the time of theft.

Knowing the specific types of data being governed is critical. In some regulations --such as HIPAA-- the lines between protected data and non-protected data can be very narrow, and even vary depending on which user or entity is currently accessing the data. Many data privacy laws give people the right to know what data is collected about them, and more specifically they can often request that data collectors provide them visibility Dor delete the information altogether. The idea is that consumers shouldn’t have to spend hours opting-in or out of privacy clauses and data agreements for every company or service they do business with.

Some privacy laws have broad application to organizations and their suppliers, partners, vendors, or even clients. Other laws may specifically call out culpability for a specific C-Level executive or department head. Knowing who is ultimately responsible for complying with the law is key in determining the scope of compliance efforts.

How was this regulation developed? Has the regulation been revised over the years? Was there a compelling industry or government-related event that drove this regulation to be created? Knowing the background of the regulations can provide a good sense of why the law exists and may inform CISOs or Data Protection Officers about the intent(s) of those who created the law.

Knowing the specific types of data being governed is critical. In some regulations --such as HIPAA-- the lines between protected data and non-protected data can be very narrow, and even vary depending on which user or entity is currently accessing the data. Many data privacy laws give people the right to know what data is collected about them, and more specifically they can often request that data collectors provide them visibility Dor delete the information altogether. The idea is that consumers shouldn’t have to spend hours opting-in or out of privacy clauses and data agreements for every company or service they do business with.

What standards exist for data usage and handling?
Nearly every regulation contains parameters about data usage and handling. This is more than just standard cybersecurity control. These provisions can call out the ways in which organizations acquire, create, store, access, share, archive, retain, and delete information. Data reduction is often a component of data handling and involves decreasing the amount of non-critical information being collected and stored. Data privacy leaders should reshape business processes so only information relevant to their services is collected to begin with.

Some privacy laws have broad application to organizations and their suppliers, partners, vendors, or even clients. Other laws may specifically call out culpability for a specific C-Level executive or department head. Knowing who is ultimately responsible for complying with the law is key in determining the scope of compliance efforts.

What reporting is required?
Many regulations have show-cause or chain-of-custody type language that dictates organizations must not only protect data, but they must be able to prove it from a legal standpoint. In some data breaches, organizations have received lesser penalties for their ability to prove that while data was breached or stolen, it was encrypted at the time of theft.

Beyond the scope of compliance requirements, it’s also critically important to identify which data matters to the organization. Undoubtedly, regulatory data will top that list, but CISOs should also be keen on prioritizing and protecting information such as intellectual property, network architecture, client lists, pricing models, and any other number of items which fall outside the scope of regulation, yet still remain crucial to the business.
Most organizations simply don’t have a good inventory of what data exists, or where. Executives are primarily concerned with ensuring the organization continues to operate — and operate within compliance — so the idea of a major project seeking to index all types of sensitive or critical data is usually shelved for a future date.
However, developing a catalog of data usage provides frontline context to executives. For example, knowing that Sales and Marketing both touch the same data, but have drastically different use cases for applying that data is a key piece of intelligence. Storage practices, data usage, file sharing, or even policies around data retention may greatly vary across business units. Without building a master index of data risk, CISOs and the executives they support are flying blind.


Learn how Infolock can help you jumpstart or refine your data inventory program – download the Data Discovery datasheet today!
After identifying the organization’s compliance requirements and data ownership, it becomes necessary to survey the organization’s available controls. In simple terms, “controls” can refer to any number of processes, tools, or technology at the disposal of the organization, although CISOs may primarily be focused on the technical controls around detection and protection, which help provide visibility into data and establish protections around data.
Taking inventory of tools is a good starting point, and leaders can start by answering the following questions:











As a control framework, DataRAMP provides guidance on how to create a DRM Program that is easily understood, measured, and effective in managing all aspects of data risk. Download your copy today!